W26 VM Patcher
A toolkit for runtime patching of a custom Lua VM in mobile apps via Frida.
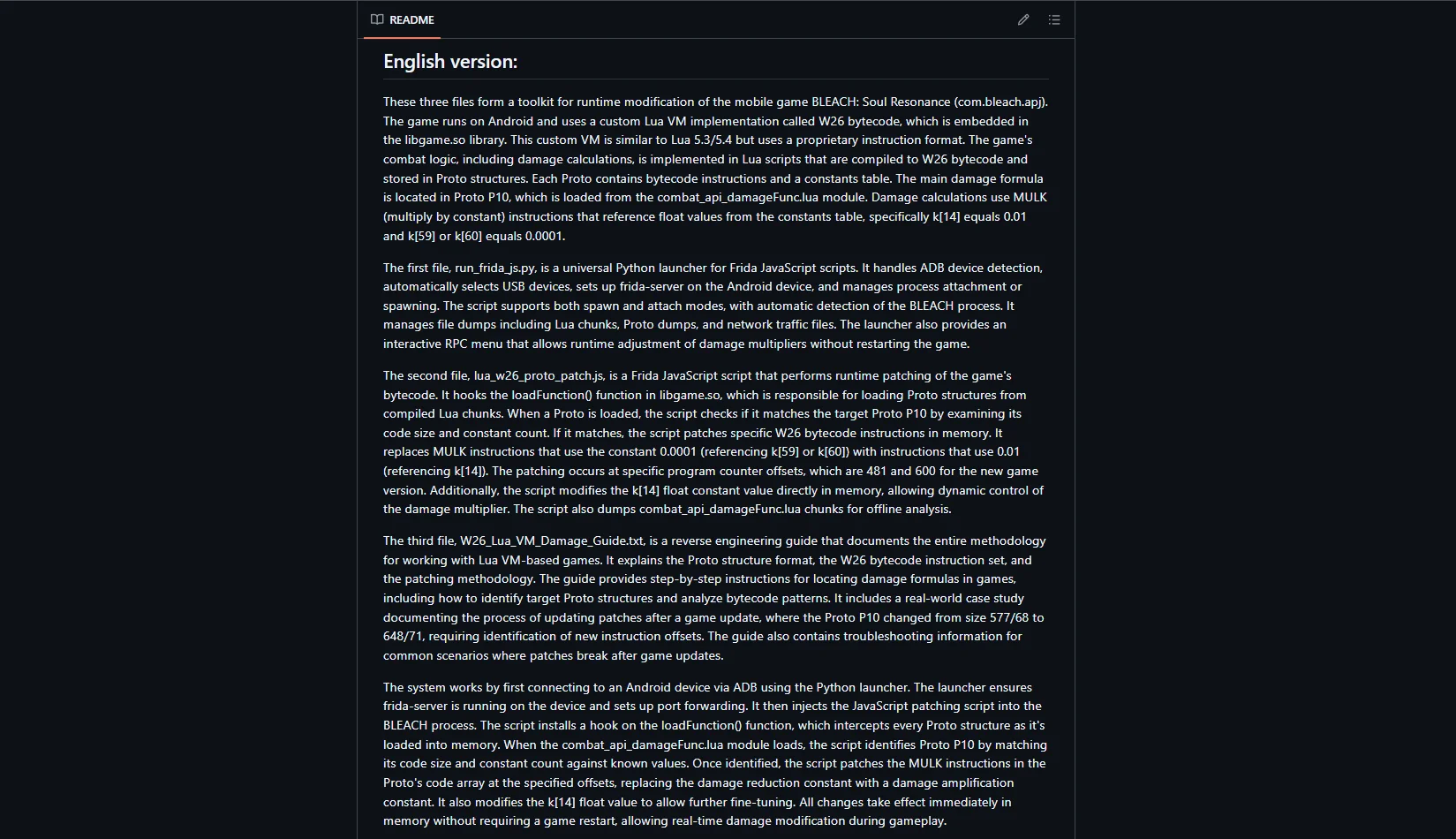
Challenge
A mobile app uses a modified Lua VM (W26 bytecode) inside the native libgame.so library. Standard analysis tools don't work with the custom bytecode format. The task was to reverse-engineer Proto structures, locate target instructions, and develop a runtime patching methodology.
Solution
Built a toolkit: W26 bytecode disassembler, Proto structure dumper, universal Frida launcher with ADB integration and RPC menu for real-time parameter tuning. The Frida script hooks loadFunction() in libgame.so and patches MULK instructions on the fly.
Your project.
Our next case study.
Tell us the challenge - we'll show you how it turns into a case with real numbers.
Start a project